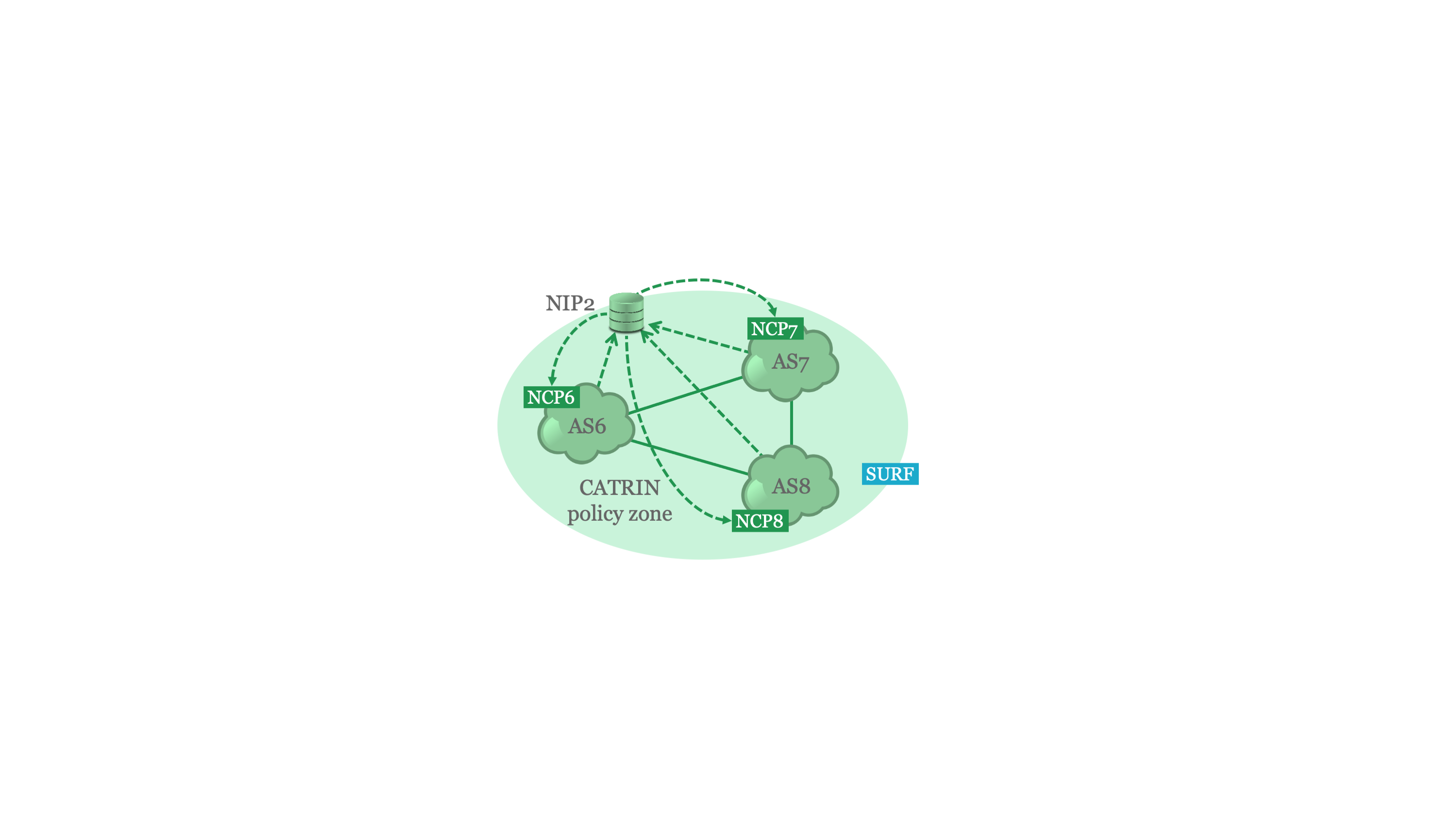
Section: CATRIN Policy Zone
Contributors: Angelos Dimoglis
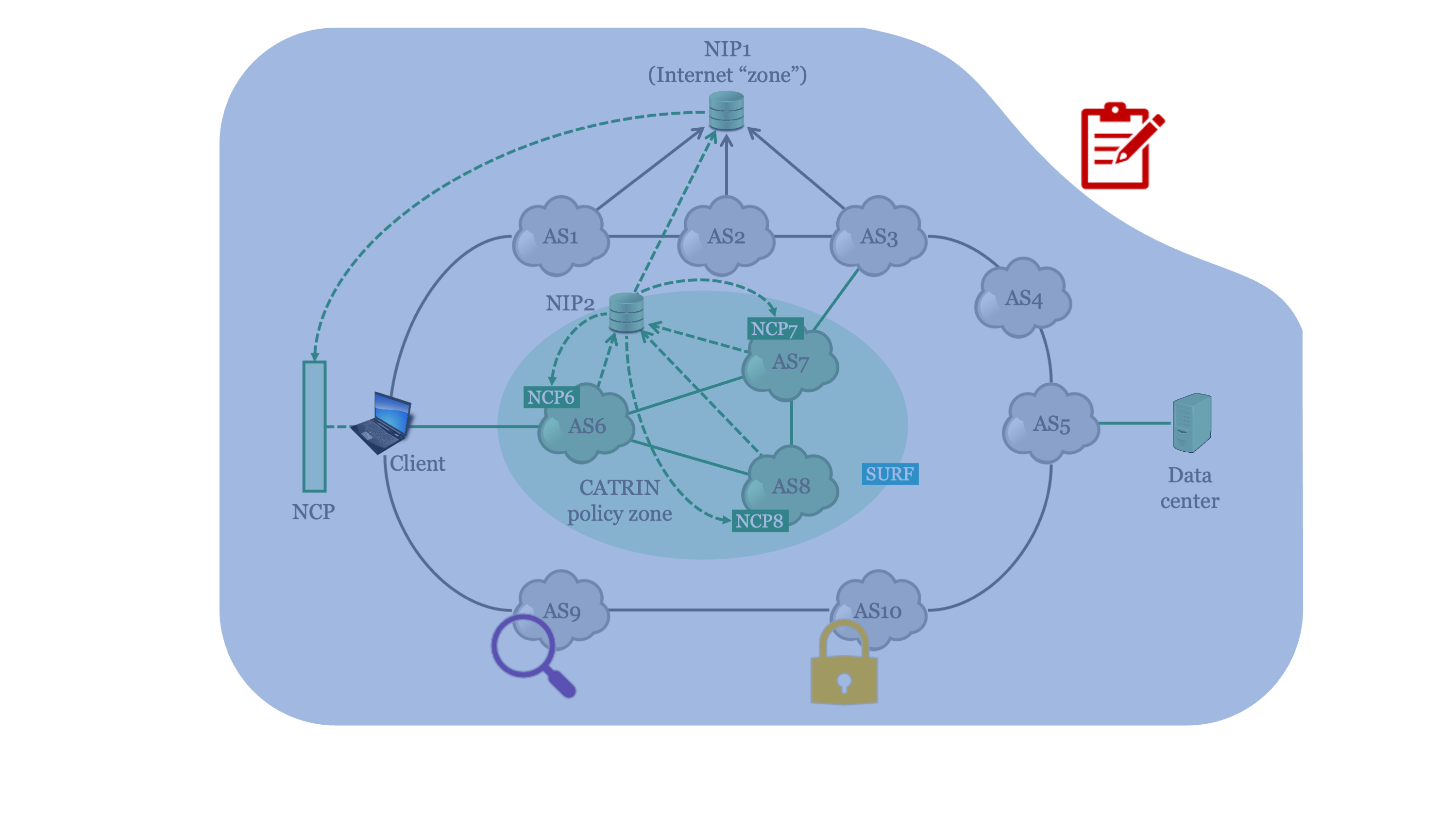
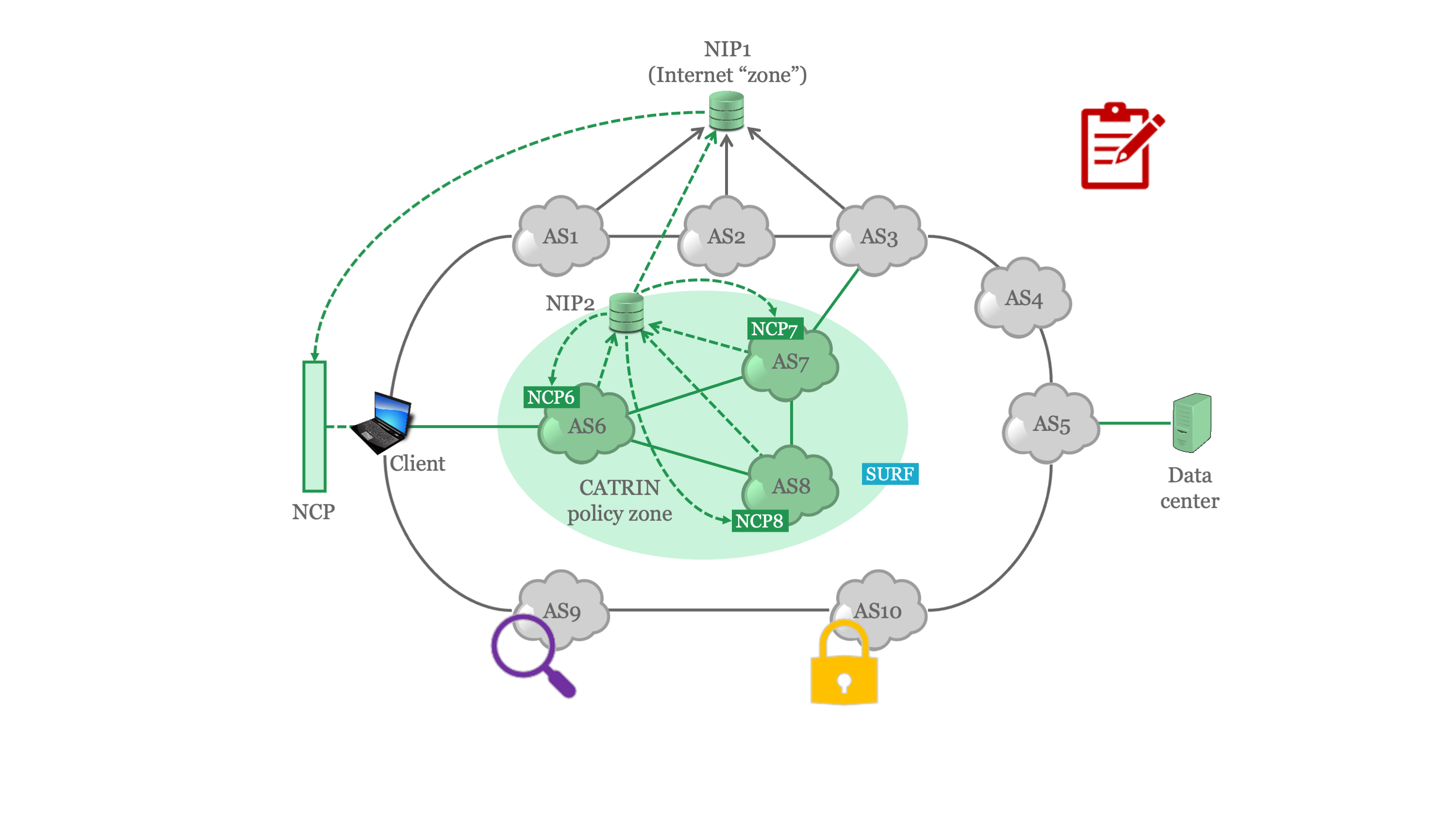
Description: CATRIN Policy Zone differs to the other options in terms of transparency and controllability. Thanks to the programmability of the networking devices we are able to collect various metadata, in order to inform the users of the used path and its trustworthiness. In-band Network Telemetry allows us to collect accurate results by encapsulating the telemetry data into the packets. Additionally, in-network control messages are used to make the necessary changes in the network to switch to a path that meets the users' requirements.
Contributors: Angelos Dimoglis
Description: CATRIN Policy Zone differs to the other options in terms of transparency and controllability. Thanks to the programmability of the networking devices we are able to collect various metadata, in order to inform the users of the used path and its trustworthiness. In-band Network Telemetry allows us to collect accurate results by encapsulating the telemetry data into the packets. Additionally, in-network control messages are used to make the necessary changes in the network to switch to a path that meets the users' requirements.
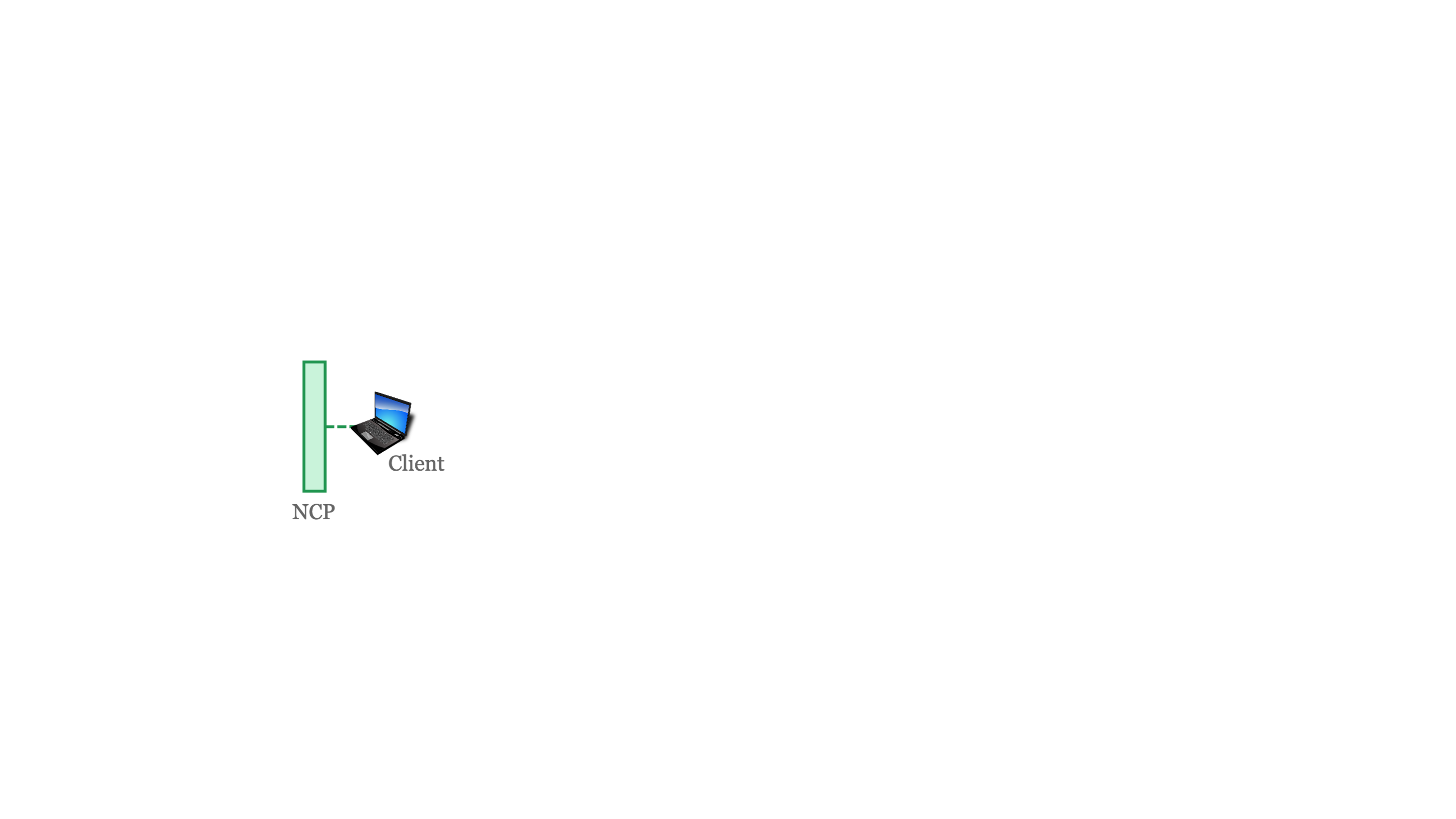
Section: Client-side NCP
Contributors: Adrian Zapletal
Description:We present an algorithm for the NCP that can be used to select a path. The central idea is that ASs can support certain features or not (e.g., protection against BGP hijacking), and users can request their data to traverse a path that fulfills certain features. Our path selection algorithm takes a graph of the network and a user request and selects the path that fulfills as many of the desired features as possible.
Contributors: Adrian Zapletal
Description:We present an algorithm for the NCP that can be used to select a path. The central idea is that ASs can support certain features or not (e.g., protection against BGP hijacking), and users can request their data to traverse a path that fulfills certain features. Our path selection algorithm takes a graph of the network and a user request and selects the path that fulfills as many of the desired features as possible.
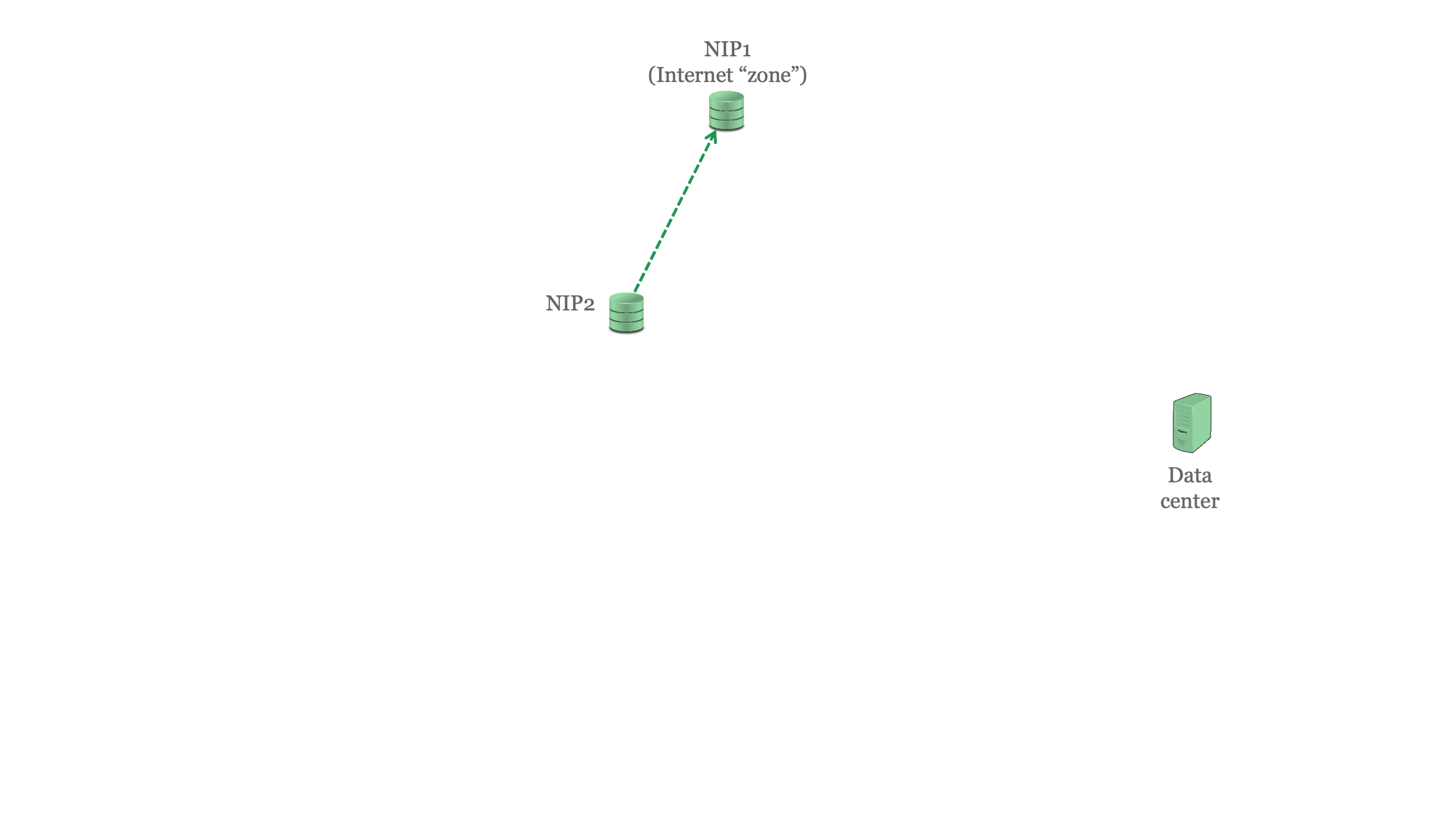
Section: NIP and measurements
Contributors: Gustavo Luvizotto Cesar
Description: We provide with a REST API to query our measurements as part of the CATRIN NIP to help its users to get insight to the Internet. We measure the Internet on a few known ports and report via the NIP those that are open. Additionally, we selected LDAP servers as a study case since such servers make part of the Internet infrastructure. LDAP offers a way to store and retrieve information about users, authenticating users, or user management in email exchange. We report via the NIP the TLS configurations and certificates of LDAP servers we establish a connection.
Contributors: Gustavo Luvizotto Cesar
Description: We provide with a REST API to query our measurements as part of the CATRIN NIP to help its users to get insight to the Internet. We measure the Internet on a few known ports and report via the NIP those that are open. Additionally, we selected LDAP servers as a study case since such servers make part of the Internet infrastructure. LDAP offers a way to store and retrieve information about users, authenticating users, or user management in email exchange. We report via the NIP the TLS configurations and certificates of LDAP servers we establish a connection.
Section: Possible paths from AS-AS and their security status
Contributors: Shyam Khadka
Description: The current Internet provides limited insights about the number of possible paths to reach from one autonomous system (AS) to another, because of the prevalence of selective announcements by the AS operators. Also, no mechanism exists to measure the security status of those possible paths. We aim to provide insights about the possible paths and the security status of those paths. We measure the security status of the paths based on multiple security metrics that the ASes on those paths are implementing, for example, Route Origin Validation (ROV) and DDoS protection. NIP can use this type of information in the CATRIN project.
Contributors: Shyam Khadka
Description: The current Internet provides limited insights about the number of possible paths to reach from one autonomous system (AS) to another, because of the prevalence of selective announcements by the AS operators. Also, no mechanism exists to measure the security status of those possible paths. We aim to provide insights about the possible paths and the security status of those paths. We measure the security status of the paths based on multiple security metrics that the ASes on those paths are implementing, for example, Route Origin Validation (ROV) and DDoS protection. NIP can use this type of information in the CATRIN project.
Section: Middleboxes present in an AS
Contributors: Bulut Ulukapi
Description: Middleboxes are essential for maintaining the modern Internet ecosystem. However, their impact on network operations has yet to be thoroughly studied. Moreover, they pose several challenges, such as introducing hidden points of failure, complicating network debugging, and creating new attack vectors for network security. Our goal is to identify middleboxes, analyze their deployment and characteristics, and conduct a security assessment to uncover potential vulnerabilities. Through this research, we aim to contribute to The Network Inspection Plane (NIP) to help users make more informed decisions. Our ultimate aim is to provide valuable insights into the functioning, behavior, and security impact of middleboxes on Internet paths.
Contributors: Bulut Ulukapi
Description: Middleboxes are essential for maintaining the modern Internet ecosystem. However, their impact on network operations has yet to be thoroughly studied. Moreover, they pose several challenges, such as introducing hidden points of failure, complicating network debugging, and creating new attack vectors for network security. Our goal is to identify middleboxes, analyze their deployment and characteristics, and conduct a security assessment to uncover potential vulnerabilities. Through this research, we aim to contribute to The Network Inspection Plane (NIP) to help users make more informed decisions. Our ultimate aim is to provide valuable insights into the functioning, behavior, and security impact of middleboxes on Internet paths.
Section: Monitoring of AS & Intrusion Detection
Contributors: Koen Teuwen
Description: Security from internet threats is a key consideration for the responsible internet. CATRIN contributes to research on Network Intrusion Detection Systems (NIDS) in several areas. Firstly, the Network Control Plane (NCP) can be used to route network traffic through middle boxes to promote visibility and ensure threats can be detected. One of our related contributions is that we identified key considerations in rule design balancing specificity and coverage. The Network Inspection Plane (NIP) can augment network security data to benefit SOC analysts. Future work may focus on new detection opportunities offered through the use of multiple middle boxes along network routes determined by the NCP.
Contributors: Koen Teuwen
Description: Security from internet threats is a key consideration for the responsible internet. CATRIN contributes to research on Network Intrusion Detection Systems (NIDS) in several areas. Firstly, the Network Control Plane (NCP) can be used to route network traffic through middle boxes to promote visibility and ensure threats can be detected. One of our related contributions is that we identified key considerations in rule design balancing specificity and coverage. The Network Inspection Plane (NIP) can augment network security data to benefit SOC analysts. Future work may focus on new detection opportunities offered through the use of multiple middle boxes along network routes determined by the NCP.
Section: Business & Policy Requirements
Contributors: Anand Siraj
Description: We study the current state of the Internet by analysing EU policies and businesses strategies. We map the policy recommendations with Controllability, Accountability and Transparency to design incentives for businesses to create the Responsible Internet. Finally, we aim to identify new business models that supports the Responsible Internet, encouraging trust and sovereignty.
Contributors: Anand Siraj
Description: We study the current state of the Internet by analysing EU policies and businesses strategies. We map the policy recommendations with Controllability, Accountability and Transparency to design incentives for businesses to create the Responsible Internet. Finally, we aim to identify new business models that supports the Responsible Internet, encouraging trust and sovereignty.
